The Internet is rife with fake and forged email. Typically these are email messages that appear to be from a friend, relative, business acquaintance, or vendor that ask you to do something. If you trust that the message is really from this person, you are much more likely to take whatever action is requested — often to your detriment.
These are forms of social engineering — the “bad guys” trying to establish a trusted context so that you will give them information or perform actions that you otherwise would not or should not do.
Here we address some of the actions you can take to protect yourself from these attacks as best as possible. We’ll present these in the order of increasing complexity / technical difficulty.
1. Viewing the actual “From” email address of email messages sent to you.
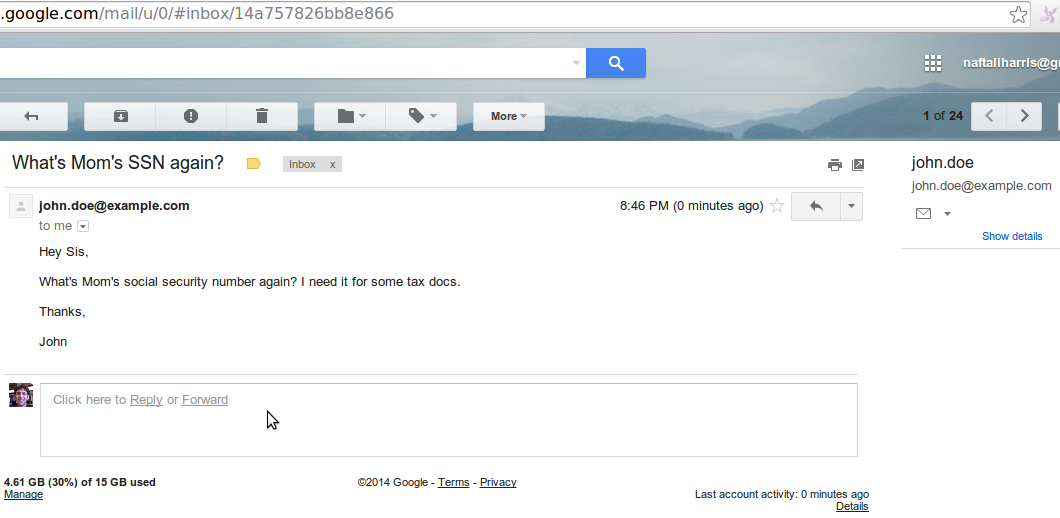
Email messages generally specify from whom they are sent. This From must include the email address of the sender and can also include any textual “name” to go with it. Many email programs by default show only the textual name and hide the actual address … for simplicity. E.g. it is perhaps easier to read “John Smith” in your message list than his actual address “kjdhkjd6876@yahoo.com”.
However, anyone technically can set these addresses and names to anything they want. So, someone can send you an email that is from any email address of their choosing and have the “name” show up as “John Smith,” or your mother’s name, or your spouse’s name, etc.
So, it is a good practice to have your email or WebMail program show the actual email address of the sender so that you can check that. This could be done in the list of messages or when you actually view the message. Don’t trust that just because a name is presented as the “From”, that the message is actually from that named person — there is no real guarantee of that (unless you take further actions we’ll discuss below).
In LuxSci WebMail, the full from name and address is displayed in the message view pane if you have it expanded (e.g. click the “+” on the left if the From, Date and Subject are displayed on a single concise line).
Additionally, you can change your preferences to “always display the email addresses of message senders and recipients instead of their names” in the WebMail message list.
2. Only view plain text previews of messages until your trust them
When you open an email message “fully”, you render its HTML content, download images, and other things. This action can inform the sender that you have read their message (see how). Once the sender knows that, they know that your email address is “good” and that you will open their messages … and so they are likely to send you more.
Additionally, it is possible that malicious messages that made it by your email filtering system may infect your computer if opened fully (e.g. due to old versions of software on your computer, newly discovered problems with your software or with images). It is best to open the message in a “plain text preview” mode first so you can evaluate if it is legitimate before opening it fully. In a plain text mode, you will not notify the senders of your actions via web bugs, and you are not opening yourself up to attacks.
3. Get a good spam and virus filter
Most good spam and virus filtering systems will detect common social engineering / forged emails that are being sent in bulk to many people on the Internet. E.g. they can stop such things as forged email from your bank asking you to login to verify your account.
These will help prevent many generic attacks, but not necessarily ones targeted directly at you or your domain / organization.
4. Get email link filtering
The most advanced email filtering systems can re-write the Internet links in your email so that when you click on them, the filtering system will scan the target page to see if it is legitimate or contains malicious content. This gives you a good measure of real-time protection against malicious links. See: prevent email phishing attacks with real-time link click protection.
If you do follow links in emails, be aware of the red flags that can tell you if a link is malicious. See the “Phishing” section of “What is Social Engineering?”
5. Use DKIM to identify forged email
DKIM is a system that cryptographically signs email messages sent and allows recipients to ensure that such messages were sent from the email servers owned by the purported sender’s organization. E.g. DKIM prevents a hacker from sending forged email … because the recipient can then easily identify it as such. Your Spam and virus filtering should use DKIM to eliminate forged email.
6. Use DKIM for your own domains
If your email service provider supports it, you should setup DKIM for your own email domains. This allows folks on the Internet to determine if email forged as coming from you is legitimate or not. It also helps you identify email that is coming in forged from yourself. See: Bounce back and backscatter spam — “who stole my email address?”
7. What about SPF?
SPF – Sender Policy Framework – is also a good mechanism to help identify if messages have originated from the trusted servers of the purported sender. It is not quite as good as DKIM, as it doesn’t prevent messages from being captured, altered, and re-sent later — those may also show up as valid.
However, as various spam filtering systems use DKIM and SPF to varying degrees, it is best to setup your domain with both SPF settings and DKIM support — and to enable both in your email filtering software.
8. Common Sense
Last but not least is use of common sense!
- Most forged email does not read exactly like messages that you normally receive from that sender … if they are your family or friend
- If there is a link to click on, hover over it first and see if the link looks funny — going to some domain that doesn’t look like it should. If so … be very wary.
- If the request is unusual or extraordinary, best to verify it with a phone call or text message or something. Many messages appear time sensitive emergencies that require you to do something to help someone, or yourself, fast. They try to use pressure and familiarity to make you skip any checking and just act out of fear or altruism. Unfortunately, you need to be skeptical until you can have some certainty that the request is legitimate….
- Even if DKIM and SPF are all OK — a messages could still be fake. E.g. a virus could have infected the sender’s computer or email account and be sending messages to his contact list through his regular servers. This will all look “Ok” on the surface and will all be valid and may even slip past your filtering software — only the content of the message itself will serve to tip you off as to its veracity – if you keep you eyes open.
If you are using LuxSci WebMail:
- We have a preference for always showing the sender email address
- We have preferences for previewing email messages (text only) and for not showing images in email right away
- We support DKIM and can assist you with setup of DKIM, SPF, and other suggestions listed herein.
