HIPAA email laws are federal privacy and security regulations that govern how healthcare organizations handle Protected Health Information (PHI) in electronic communications. The HIPAA Privacy Rule and Security Rule establish requirements for protecting patient information when transmitted via email, including encryption standards, access controls, and audit procedures. Healthcare organizations must implement appropriate safeguards to prevent unauthorized disclosure of patient information through email communications while maintaining compliance with federal regulations. Email communication in healthcare requires careful attention to privacy laws that protect patient confidentiality. Understanding HIPAA email laws helps healthcare organizations communicate effectively while avoiding violations and penalties.
How Do HIPAA Email Laws Protect Patient Information?
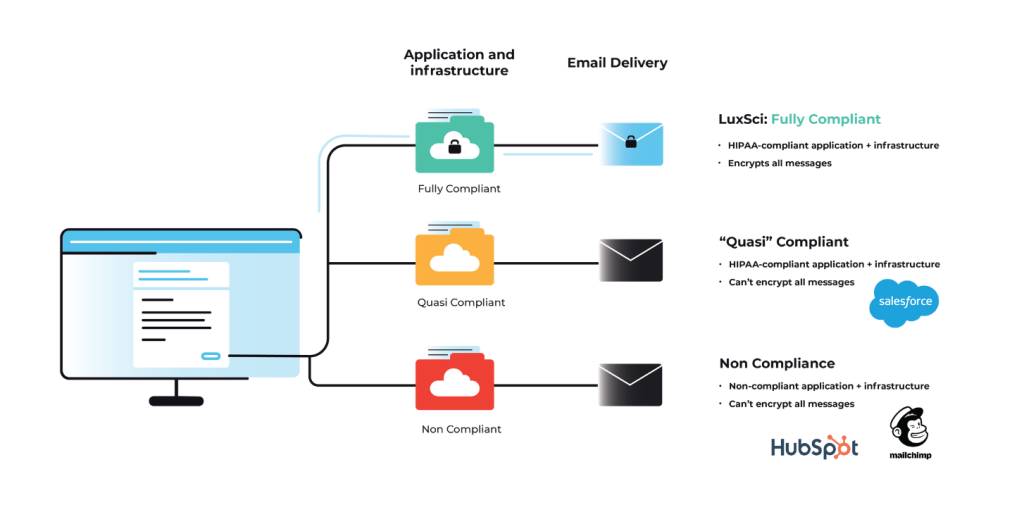
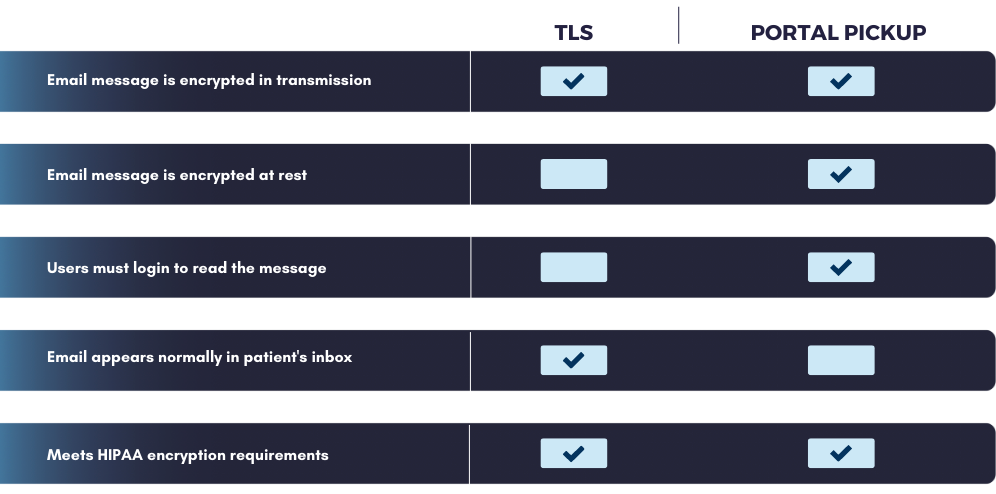
Patient information receives protection through strict limitations on email usage and disclosure requirements under federal privacy regulations. Healthcare organizations cannot freely share patient data via email without implementing security measures that prevent unauthorized access or interception. HIPAA email laws require covered entities to assess risks associated with email communications and implement safeguards appropriate to their operational environment. Encryption requirements form a cornerstone of email protection under HIPAA regulations, though the Security Rule treats encryption as an addressable specification rather than a mandatory requirement. Organizations must evaluate whether encryption is reasonable and appropriate for their email communications containing patient information.
Most healthcare organizations implement email encryption to protect against data breaches and demonstrate compliance with federal security standards. Access control provisions limit who can send, receive, or access emails containing patient information within healthcare organizations. Staff members need unique user credentials and role-based permissions that restrict email access to information necessary for their job functions. Automatic logoff features prevent unauthorized access when devices are left unattended. Audit requirements mandate that healthcare organizations monitor and log email system activity to track potential security incidents or privacy violations. HIPAA email laws require documentation of who accessed patient information, when access occurred, and what actions were performed. Organizations must maintain these audit logs and review them for suspicious activity or compliance gaps.
What Email Practices Violate HIPAA Laws?
Sending unencrypted emails containing patient information to external recipients violates HIPAA security standards in most circumstances. Healthcare organizations cannot email lab results, treatment summaries, or other PHI to patients using standard email without encryption protection. External communications require additional security measures to prevent unauthorized interception during transmission. Using personal email accounts for work-related patient communications creates multiple compliance violations under HIPAA regulations. Healthcare workers cannot forward patient information to personal Gmail, Yahoo, or other consumer email accounts that lack appropriate security controls. Personal email usage also creates challenges for audit logging and organizational oversight of patient information handling.
Sharing patient information with unauthorized recipients through email represents a serious privacy violation that can result in substantial penalties. Staff members cannot email patient details to family members, colleagues outside the care team, or external parties without proper authorization. Accidental disclosure through incorrect email addresses or reply-all mistakes can also constitute HIPAA violations. Inadequate access controls that allow broad email system access violate HIPAA requirements for limiting PHI exposure to minimum necessary levels. Organizations cannot provide all staff members with access to patient email communications regardless of their job responsibilities. Role-based restrictions must limit email access to information required for specific work functions.
How Can Healthcare Organizations Comply With HIPAA Email Laws?
Risk assessment procedures help healthcare organizations evaluate their email systems and identify compliance gaps that need attention. Organizations examine current email practices, security controls, and staff training to determine where improvements are needed. The assessment process guides development of policies and procedures that address specific risks identified within the organization’s email environment. Staff education programs ensure that healthcare workers understand their responsibilities under HIPAA email laws and know how to handle patient information appropriately. Training covers email security best practices, encryption requirements, and procedures for reporting potential violations.
Healthcare organizations need ongoing education to keep staff current with evolving regulations and technology changes. Technology implementation supports compliance through automated security features that protect patient information without requiring constant user intervention. Healthcare organizations can deploy email encryption systems, data loss prevention tools, and access management platforms that enforce HIPAA email laws. Automated systems reduce reliance on staff compliance and provide consistent protection for patient communications. Policy enforcement mechanisms ensure that HIPAA email laws are followed consistently across healthcare organizations. Clear policies define acceptable email practices, specify security requirements, and outline consequences for violations. Organizations need monitoring procedures to verify policy compliance and corrective action processes to address violations when they occur.