Digital technologies have entirely shifted how individuals want to interact with their healthcare providers. As consumers have become used to emailing or texting with their hairstylists, mechanics, and other providers to schedule appointments, they want to have the same level of interaction with their healthcare providers.
However, many healthcare organizations find it challenging to deliver the same experience because of their compliance requirements under HIPAA. They must balance usability and access with security and patient privacy. To send secure emails, they often resort to secure web portals.
Problems with Secure Web Portals
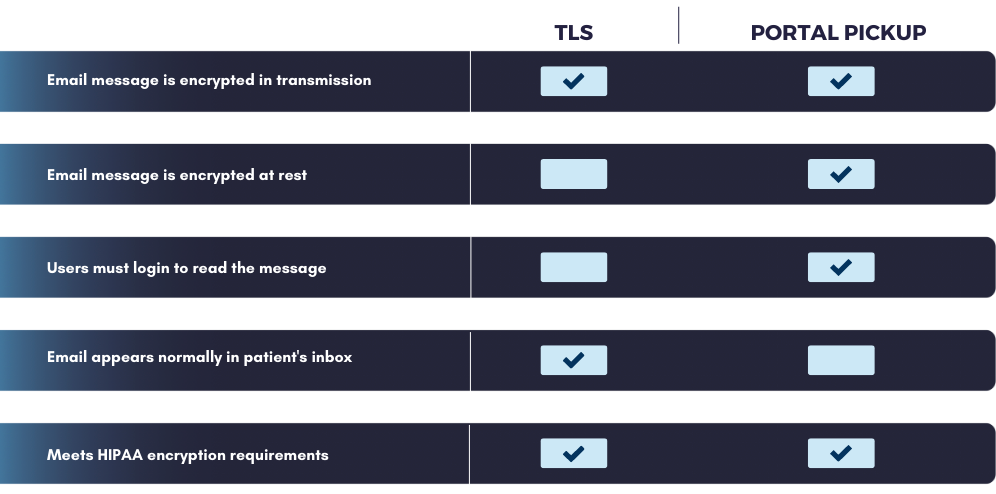
One of the most common ways that healthcare organizations communicate securely with patients is by using the secure web portal method of email encryption. In this scenario, messages are sent to a secure web server, and a notification is sent to the recipient, who then logs into the portal to retrieve the message.
While highly secure, this method is not popular with recipients because of the friction it creates.
To maintain a high level of security, users must log in to a separate account to retrieve the message. This extra step creates a barrier, especially for individuals who are not tech-savvy. In addition to creating a new account, they must remember a different username and password to access their secure messages. If the recipient doesn’t have this information readily available, they will likely delete the message and move on with their day. Many users will never bother logging in because of the inconvenience. This creates issues for organizations that want to use email for standard business communications and patient engagement efforts.
While this method may be appropriate for sending highly sensitive information like medical records, financial documents, and other valuable information, many emails that must meet compliance requirements only infer sensitive information and do not require such a high level of security. Flu shot reminder emails are not as sensitive or potentially devastating as sending the wrong medical file to someone. Healthcare organizations need to use secure email solutions that are flexible enough to send only the most sensitive emails to the portal and less sensitive emails using other methods.
How to Meet Compliance Requirements for Sending Secure Email
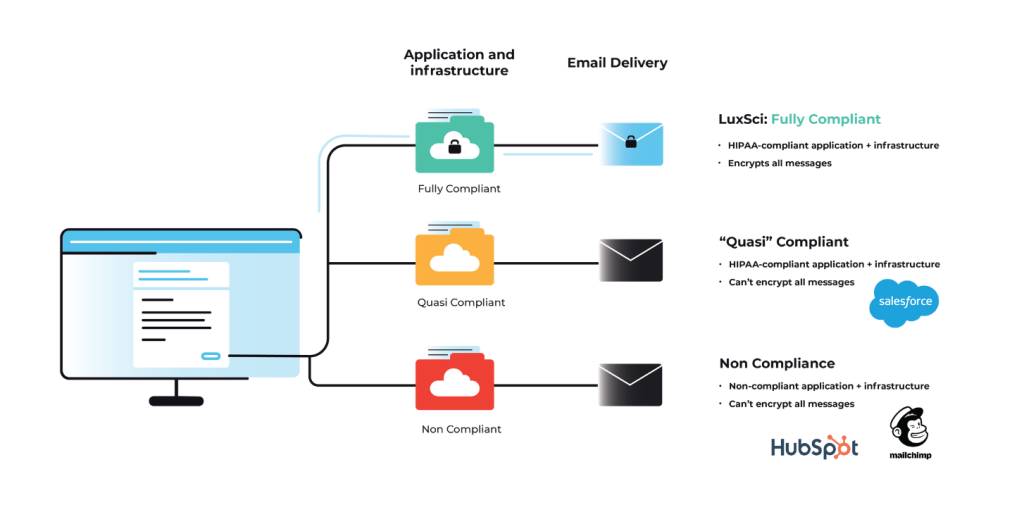
So, what other options do you have for sending secure emails? The answer will depend on what specific requirements you need to meet. Healthcare organizations that must abide by HIPAA regulations will find a lot of flexibility regarding the technologies they can use to protect ePHI in transit.
In addition to a secure web portal, three other types of encryption are suitable for email sending: TLS, PGP, and S/MIME. PGP and S/MIME are more secure than a web portal. They also require advanced technological skills and coordination with the end-user to implement, which makes them impractical for most business email sending.
That leaves us with TLS, which is suitable to meet most compliance standards (including HIPAA) and delivers an email experience much like that of a “regular” email.
Send Secure Emails with TLS Encryption
TLS encryption is an excellent option for secure email sending that provides a seamless experience for the recipient. Emails sent securely with TLS appear like regular, unencrypted emails in the recipient’s inbox.
TLS encrypts the message contents as they travel between mail servers to prevent interception and eavesdropping. Once the message reaches the inbox, it is unencrypted and can be read by anyone with access to the email account. For this reason, it is less secure than a portal but secure enough to meet compliance requirements like HIPAA.
If you’re wondering why this is, HIPAA only requires covered entities and business associates to protect PHI when it is stored on their systems or as it is transmitted elsewhere. After the message reaches the recipient, it is up to the recipient to decide what they want to do to secure the information. HIPAA does not apply to individuals. Each person is entitled to share and store their health information however they see fit.
Conclusion
Balancing security and usability is a significant challenge for healthcare organizations. If the message is too secure, it may be difficult for the recipient to open and engage with it. If it’s not secure enough, it is too easy for cybercriminals and other bad actors to intercept private information as it is sent across the internet.
Choosing an email provider like LuxSci, which offers flexible email encryption options, allows users to choose the right level of encryption for each message to maximize engagement and improve health outcomes. Contact our team today to learn more about how we can support your efforts.