Effective patient engagement is increasingly becoming a top priority for many healthcare organizations – and for good reason.
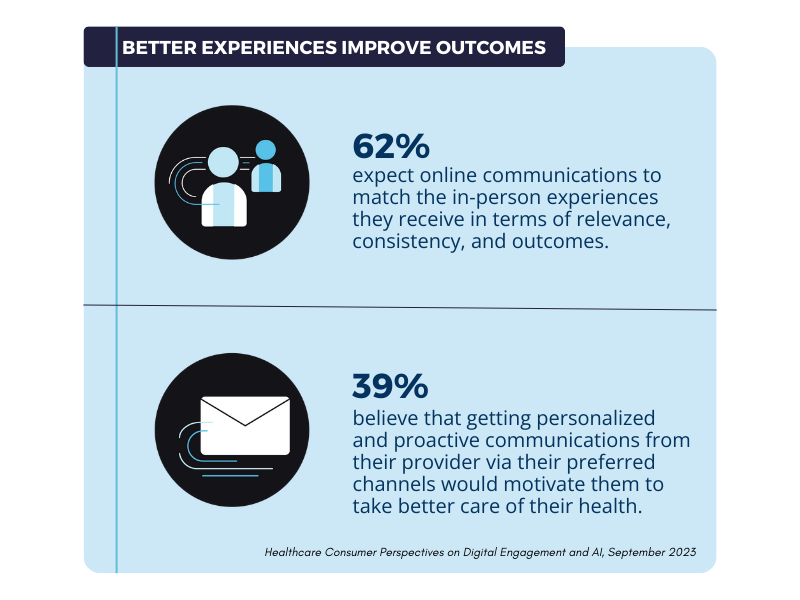
First and foremost, the more a patient or customer is engaged in their healthcare journey, the better their health outcomes and quality of life. With increased communication and engagement, patients are more likely to have potential conditions diagnosed sooner, take preventative measures to prevent illnesses, and educate themselves on ways to manage and improve their health.
However, the benefits don’t end there and aren’t restricted to the patient. Engaged patients pay bills faster, are more open to new products and services, and report higher levels of satisfaction with the companies that contribute to their health and well being. For healthcare providers, payers, and suppliers, this results in higher revenue, more opportunities for growth, and the attainment of long-term organizational goals.
Digital Patient Engagement Is Easier than Ever
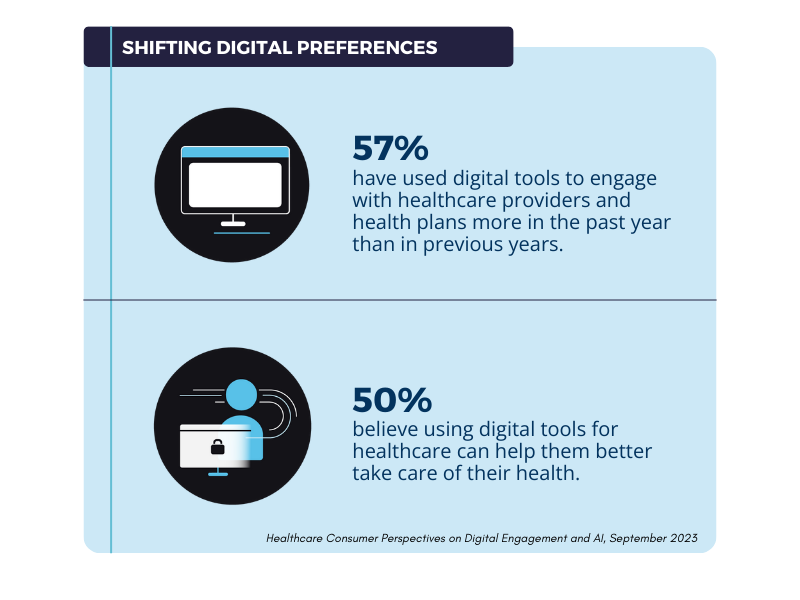
Fortunately, advances in technology and their rapid adoption by patients and customers (expedited by the COVID-19 pandemic) have made it easier for healthcare organizations to achieve successful digital interactions and engagement. Healthcare companies have more tools and channels than ever before to help conduct personalized engagement campaigns that meet patients on their terms, making it easier to capture their attention. Secure email takes it even further with the ability to include protected health information in messages to personalize
Despite these advancements, however, there are still several barriers that prevent healthcare companies from engaging with patients and reaping the associated benefits. Fortunately, each barrier can be overcome to help patients and customers feel more included and instrumental in their healthcare journeys.
With this in mind, this post discusses the main barriers to digital patient engagement and how to overcome them to drive better healthcare outcomes for your patients and growth for your organization.
The Main Barriers To Digital Health Engagement
The four key barriers to digital health engagement that we’ll explore in this post are as follows:
-
- Low Health Literacy
-
- Privacy And Security Concerns
-
- Age And Cultural Differences
-
- Lack Of Personalization
Let’s review each barrier in turn, while offering potential solutions that will contribute to greater digital health patient engagement for your healthcare organization.
Low Health Literacy
The first barrier to successful digital health patient engagement is your patients having insufficient health or medical knowledge. Healthcare is laden with terminology, including medical conditions, pharmaceuticals, the human anatomy, and many patients simply don’t understand enough to get more involved with their healthcare journey. Worse still, few patients will admit they don’t understand, as people are often embarrassed at their lack of knowledge.
Consequently, if your digital health patient engagement campaigns are heavy with medical jargon and lack personalization, patients won’t act on the information to drive better outcomes.
Solution: Create Educational Health Content
Develop simple educational resources for your patients that apply to their unique needs and condition. This will help them understand their state of health and make better sense of subsequent communications they’ll receive from you and their other healthcare providers.
This educational content could be in the form of periodic email newsletters, giving you a great reason to keep in touch with your patients. Alternatively, they could take the form of blog posts or articles on a patient portal, which could be supported by an email marketing campaign to let patients know about the article. In helping to increase your patients’ health literacy, you offer additional value as a healthcare provider, payer or supplier.
Additionally, keep the medical jargon in your email communications and other patient engagement channels to a minimum. Empathize with the fact that some patients won’t understand as much as others when it comes to healthcare provision and explain things as plainly as possible.
Data Privacy And Security Concerns
Unfortunately, due to its sensitivity and critical nature patient data, i.e., protected health information (PHI) is highly prized by cybercriminals. Subsequently, there have been many high-profile healthcare breaches, such as the Change Healthcare breach, in early 2024, which affected 100 million individuals, that make patients increasingly wary about sharing health-related information via email, text, or other digital communication channels.
That said, their wary attitude is the right one to adopt, but not at the expense of enhancing engagement and improving their health outcomes.
Solution: Invest In HIPAA Compliant Communication Tools
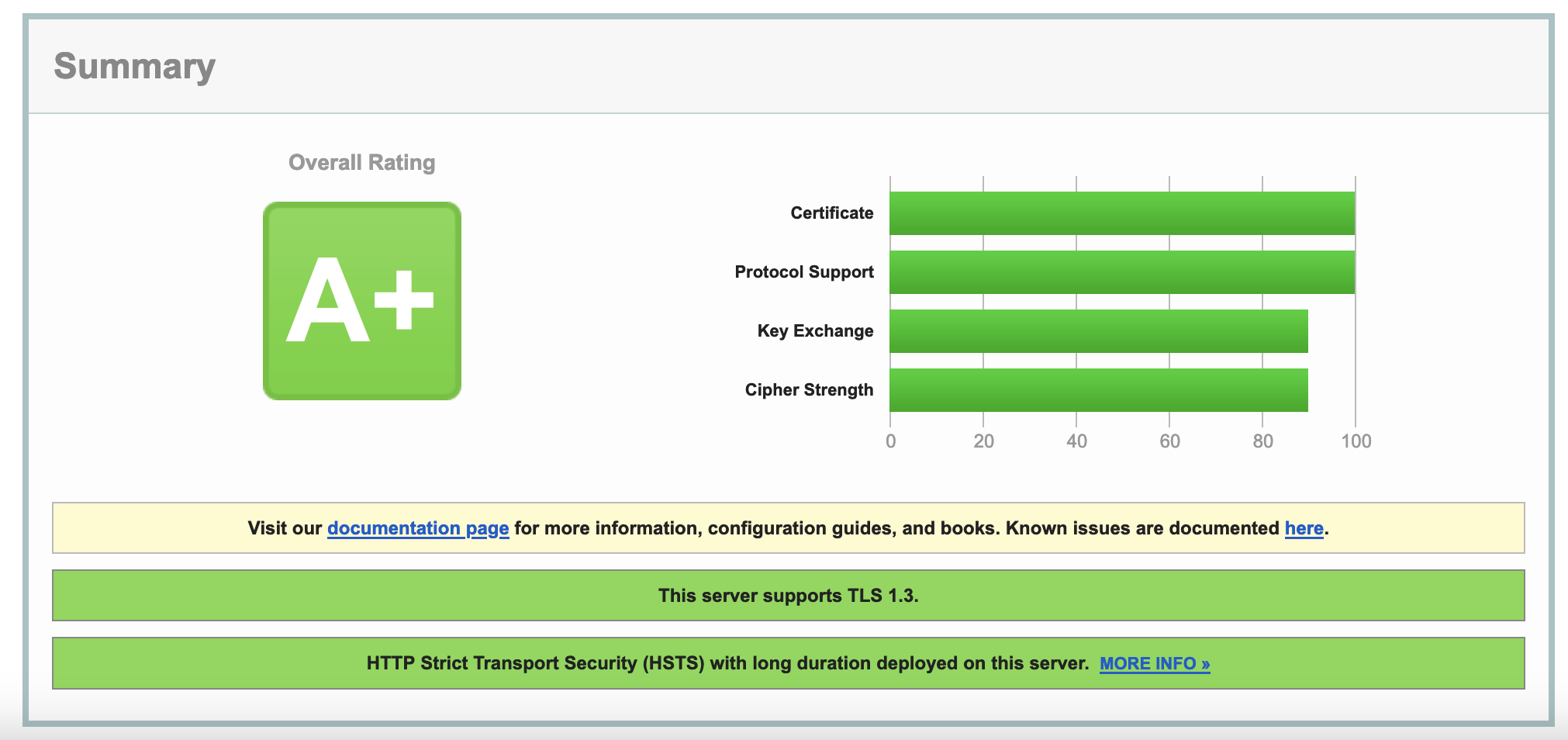
Ensure that the digital tools you use to engage with patients possess the security features required for HIPAA compliance. The Health Insurance Portability and Accountability Act (HIPAA) provides a series of guidelines that healthcare organizations must comply with to best safeguard PHI. Consequently, solutions that promote their commitment to HIPAA compliance, such as LuxSci, will understand the privacy, security, and regulatory needs of healthcare companies and have developed their tools accordingly.
Most importantly, a HIPAA compliant vendor will sign a Business Associates Agreement (BAA), the legal documentation that outlines your respective responsibilities regarding the protection of PHI. Safe in the knowledge that the patient data under your care is secure, you can concentrate your efforts on personalizing your digital communication campaigns for maximum effect.
Age And Cultural Differences
Ineffective patient engagement efforts (or a complete lack of engagement, altogether) can reinforce cliches about the use of digital tools within particular patient groups. The reality, however, is that many healthcare organizations don’t account for age differences and channel preferences in their patient engagement strategies.
Subsequently, if you only engage with patients on a single communication channel, you risk alienating others because it’s not their medium of choice.
Solution: Adopt a Multi-Channel Engagement Strategy
Instead of focusing on one communication medium, diversify your approach and adopt a multi-channel engagement strategy. This could encompass email, SMS, and phone outreach, for instance. This covers the more proverbial bases and gives you a chance to engage with patients on their preferred terms.
Lack Of Personalization
One of the main reasons that healthcare organizations fail to engage with their patients is that they adopt a “one-size-fits-all” approach, attempting to craft communications that appeal to as many people as possible. Unfortunately, this has the opposite of the desired approach, not connecting anyone in particular and engaging few patients as a result.
Solution: Personalize Your Patient Engagement Campaigns with PHI
With a HIPAA compliant solution, you can use PHI to personalize patient engagement, leveraging their health data to craft messaging that reflects their specific condition, needs, and where they are along their healthcare journey. PHI also can be used to segment patients into subgroups, grouping them by specific commonalities such as age, gender, health condition, and lifestyle factors.
Successful Digital Health Patient Engagement with LuxSci
With more than 20 years of experience in delivering secure digital healthcare communication solutions to some of the world’s leading healthcare providers, payers and suppliers, LuxSci is a trusted partner for organizations looking to boost their patient engagement efforts, while protecting patient data and remaining compliant at all times.
LuxSci’s suite of HIPAA compliant solutions include:
-
- Secure Email: HIPAA compliant email solutions for executing highly scalable, high volume email campaigns that include PHI – millions of emails per month.
-
- Secure Forms: Securely and efficiently collect and store ePHI without compromising security or compliance – for onboarding new patients and customers and gathering intelligence for personalization.
-
- Secure Marketing: proactively reach your patients and customers with HIPAA compliant email marketing campaigns for increased engagement, lead generation and sales.
-
- Secure Text Messaging: enable access to ePHI and other sensitive information directly to mobile devices via regular SMS text messages.
Interested in discovering more about LuxSci can help you upgrade your cybersecurity posture for PHI and ensure HIPAA compliance? Contact us today!