MailHippo is considered HIPAA compliant when healthcare providers use a paid plan or 30-day free trial, sign a BAA, and enable the required security settings. As a result, MailHippo HIPAA compliant usage is only possible when all of these conditions are met. The cloud-based encrypted email service provides secure messaging for healthcare providers handling PHI, though considerations should be made in areas such as administrative controls, audit logging, and integration options. Healthcare providers considering MailHippo for patient communications should examine its security capabilities alongside potential workflow capabilities before making a decision on implementation.
Email Security Requirements Under HIPAA
Healthcare email systems handling PHI must satisfy federal privacy regulations through encryption, access controls, and audit capabilities. Data encryption during transmission prevents unauthorized interception of patient information traveling across public networks. Storage encryption protects archived messages containing health data while they reside on email servers. Access restrictions ensure that only authorized personnel can view patient communications relevant to their job responsibilities.
Audit controls track who accesses email systems, what messages they view, and when these activities occur. Integrity safeguards prevent unauthorized modification or deletion of patient communications that might compromise medical records or compliance evidence. Business associate agreements create legal frameworks defining how email service providers protect patient information and respond when security incidents occur.
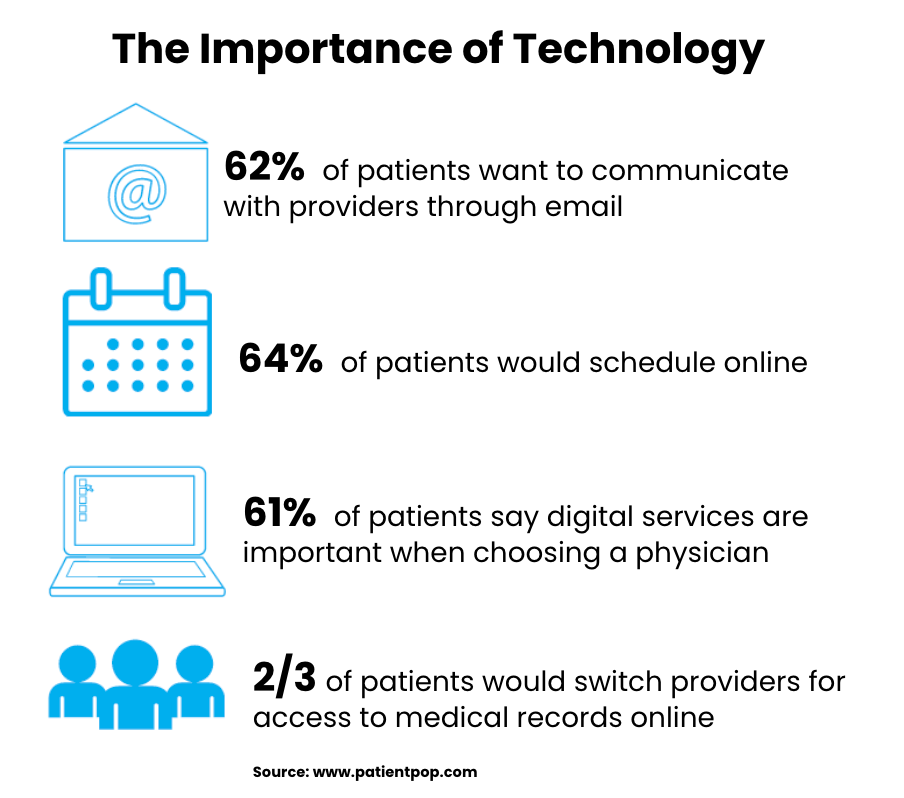
Consumer email platforms lack typically these protections in their standard configurations, creating compliance vulnerabilities when healthcare providers use them for patient communications. For example, Gmail, Outlook, and Yahoo Mail were designed for general business use rather than regulated healthcare environments. To summarize, healthcare organizations benefit from email services that implement HIPAA security requirements by design rather than requiring complex manual configurations that might be implemented incorrectly.
The MailHippo Service Model
MailHippo positions itself as a straightforward encrypted email solution for professionals in regulated industries including healthcare, legal, and financial services. The cloud-based platform eliminates time-consuming software installation requirements, allowing users to send secure messages through web browsers without downloading applications. This simplicity appeals to solo practitioners and small medical practices that lack dedicated IT support staff.
Independent healthcare providers, small medical offices, mental health professionals, and insurance consultants represent the service’s primary user base. These smaller operations value ease of use over advanced features, preferring solutions that deliver basic security without complicated setup and user procedures. It’s important to note that MailHippo delivers encrypted messages to recipients through secure web portals rather than standard email clients, creating protected communication channels that don’t require recipients to install special software.
The MailHippo service model focuses on one-to-one secure messaging rather than bulk communications or automated workflows. Healthcare providers send individual messages to patients or colleagues through encrypted channels that protect information during transmission and storage. Recipients receive notifications that secure messages await them in web portals where they can view content after authentication. This approach works for routine patient communications but may not support more complex healthcare communication needs. For larger organizations that prefer users staying within a dedicated email application or need high volume sending, several HIPAA compliant alternatives exist, including LuxSci.
MailHippo’s HIPAA Compliant Encryption and Security Features
MailHippo features transport encryption using TLS protocols, protecting messages during transmission between email servers, and preventing interception while communications travel across networks. AES-256 encryption secures stored messages, ensuring that archived communications remain protected if servers are compromised. The combination of transmission and storage encryption addresses HIPAA requirements for protecting ePHI throughout its lifecycle.
Recipient access through secure web portals eliminates the vulnerabilities associated with delivering encrypted content through standard email clients. Patients and healthcare providers authenticate themselves before viewing message content, creating additional security layers beyond basic encryption. Using a portal-based approach reduces exposure through compromised email accounts or insecure devices that might not maintain proper security configurations.
Authentication requirements mandate that users log in before sending or receiving messages, preventing unauthorized access to patient communications. MailHippo supports two-factor authentication (2FA), but the company’s documentation doesn’t clearly spell out which MFA methods are available or whether organizations can enforce MFA for all users. Healthcare entities that require strong authentication factors, such as hardware tokens or biometrics should confirm these details directly with the vendor.
Delivery and read receipts provide tracking information about message transmission and recipient access. These receipts confirm that messages reached intended recipients and document when recipients viewed content. The tracking capabilities, while useful for confirming communication delivery, lack the detailed audit logging that larger healthcare organizations likely need for compliance and security investigations.
Third-Party Email Provider Contract Requirements
Federal regulations classify email service providers handling PHI as business associates subject to HIPAA compliance obligations. Healthcare entities must execute written agreements with these providers defining responsibilities for protecting patient data and responding to security incidents. Without signed BAAs, email communications containing patient information violate HIPAA regardless of encryption or other security measures implemented.
MailHippo HIPAA compliant email requires executed business associate agreements between the service provider and healthcare organizations. MailHippo indicates that it provides a HIPAA Business Associate Agreement (BAA) as part of its service offerings; organizations should confirm BAA availability and execution terms before transmitting protected health information.
Business associate agreements specify encryption standards, incident notification timelines, and procedures for handling patient data when service relationships terminate. These contracts allocate liability between healthcare organizations and email providers, protecting organizations from financial exposure when security breaches that result from provider negligence. Agreement terms should address data retention requirements, geographic restrictions on information storage, and secure deletion methods when retention periods expire.
Healthcare organizations implementing MailHippo HIPAA compliant solutions must verify that executed agreements cover all anticipated uses of the platform. Agreements should explicitly permit transmission and storage of PHI while defining what security measures the provider maintains. Without proper agreements in place, healthcare organizations assume full liability for any security incidents involving patient communications transmitted through the platform.
Administrative Control & Potential Limitations
User management capabilities determine how healthcare organizations control access to email systems and enforce security policies across multiple staff members. Role-based permissions enable organizations to grant different access levels to physicians, nurses, administrative staff, and billing personnel based on their job functions. Centralized administration consoles allow IT staff or practice managers to oversee all user accounts, modify permissions, and review security concerns from a single interface.
MailHippo HIPAA compliant implementations may lack the administrative tools that larger healthcare organizations require, including managing large numbers of users. The platform does not provide role-based permission structures that restrict access based on job functions or patient care relationships. Centralized dashboards for overseeing user activities across organizations are absent, making it more difficult for administrators to monitor security compliance or identify potential policy violations.
Integration & Workflow Considerations
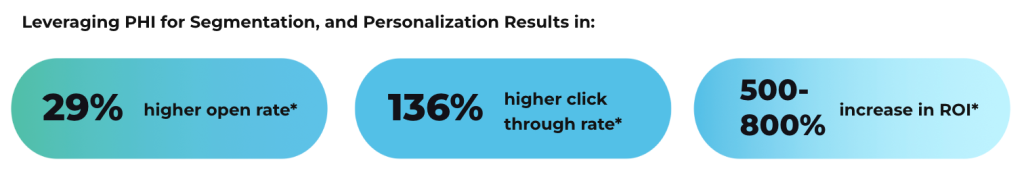
Healthcare communication workflows rely heavily on integration between email systems, electronic health records, practice management software, and patient engagement platforms. Automated workflows reduce administrative burden while ensuring consistent security practices across all patient communications. API connectivity enables different healthcare applications to exchange information seamlessly without requiring manual data transfer, which increases the risk of human error.
While MailHippo publishes an email API, it does not offer ‘out-of-the-box’ integration capabilities with electronic health record systems or practice management platforms. As a result, healthcare organizations cannot automatically populate patient communications with appointment information, test results, or treatment updates from their clinical systems without technical integration work.
Marketing automation and bulk communication capabilities do not exist within the MailHippo service model, which is designed for individual message transmission. Healthcare organizations conducting patient outreach, appointment reminders, or health education campaigns need alternative solutions for these activities. The focus on one-to-one messaging limits the platform’s utility for organizations with diverse communication requirements high-volume sending needs beyond routine secure messaging.
Appropriate Use Cases and Organizational Fit
Solo practitioners and small medical practices with straightforward communication needs represent ideal candidates for MailHippo HIPAA compliant email. These organizations likely value simplicity over advanced features, preferring solutions that deliver basic security without requiring technical expertise to configure and maintain. Single physicians or therapists communicating with individual patients benefit from the portal-based secure messaging that protects patient information without complicated setup procedures.
Healthcare providers requiring only basic one-to-one secure messaging without forms, complex integrations, or user management can operate effectively within the platform’s capabilities. For example. mental health professionals conducting therapy practices, independent consultants providing healthcare advice, and small specialty clinics with limited communication volumes fit the service model well.
Larger healthcare organizations, multi-location practices, and operations with complex communication requirements and workflows will find the platform’s limitations constraining. Organizations needing multiple user tiers, departmental segregation, or centralized administration lack the tools necessary for managing these structures. Healthcare systems requiring electronic health record integration, automated workflows, or bulk communication capabilities often need more comprehensive email security platforms than MailHippo HIPAA compliant setups can provide.
Implementation and Compliance Verification
Now, it’s important to note that healthcare organizations implementing secure email must verify that all HIPAA requirements are satisfied before transmitting PHI. Proper configuration helps ensure that encryption activates properly, access controls function as intended, and audit logging captures necessary security events. In addition, business associate agreement execution creates legal frameworks before any patient data flows through email systems.
As with any ESP for healthcare, organizations adopting MailHippo HIPAA compliant email should document their compliance measures, including executed agreements, security configurations, and staff training records. Documentation demonstrates due diligence during regulatory audits while providing evidence that organizations took appropriate steps to protect patient information. Policy development establishes guidelines about what information can be transmitted via email and what alternative communication methods should be used for particularly sensitive content.
Staff training prepares healthcare workers to use secure email systems properly while maintaining patient privacy throughout communications. Training should cover portal access procedures, recipient verification methods, and appropriate content guidelines that prevent inadvertent disclosures. Documented training records prove that organizations educated staff about security requirements before granting email system access.
Finally, periodic security assessments verify that email systems continue meeting compliance requirements as technology and threats evolve. Assessment schedules should include configuration reviews, access control testing, and verification that business associate agreements remain current. Healthcare organizations relying on MailHippo HIPAA compliant workflows must treat email security as an active process rather than a one-time setup, maintaining vigilance about vulnerabilities and regulatory changes.
If you’d like to learn more, reach out to us today!